Interfacing with 500+ Security and Engineering Directors, I see an urgent need for compliance support.
A need that was not as urgent or disproportionately dependent on the Engineering Teams when I was an Engineering Leader at Cisco.
Pre-pandemic, compliance was not seen as a function that was supported by engineering leaders, instead compliance efforts for a few schemes were outsourced.
Yet the post-pandemic compliance world is now more outcome-driven, demanding enterprises sustain and improve past compliance achievements like PCI DSS 2.0 while also moving forward with newer regulatory requirements across multiple jurisdictions, such as NIS2, the US National Cybersecurity Strategy, and the European Cyber Resilience Act.
One such mandate is the Digital Personal Data Protection Act, a bill passed in the Indian Parliament, containing core provisions defining personal data use, collection, and governance.
All enterprises collecting and processing data of Indian citizens are to comply with this.
Failure to do so will induce penalties amounting to upwards of ₹250 Crores and brand erosion from one of the largest consumer markets in the world.
So, the expectation is not just to shoulder the regulatory responsibilities but also to do them cost-efficiently since current methods are known to overrun allotted budgets by 60% or more.
In this blog, I will outline the core provisions of this mandate and the cultural shifts that will guarantee a smooth, jurisdiction-agnostic, effective, and ROI-positive capacity building.
TL;DR
The DPDP Act is India's data privacy law that holds every enterprise processing Indian citizens' data accountable with penalties exceeding ₹250 Crores for non-compliance. Data of 518 million Indians is already on the dark web. Manual compliance overruns budgets by 60%. The faster you act, the less it costs.
DPDP Compliance Checklist
Internet penetration in India has been on a steep rise since 2016.
Starting from 400 million users in 2016, Internet users more than doubled to 954.40 million in March 2024.
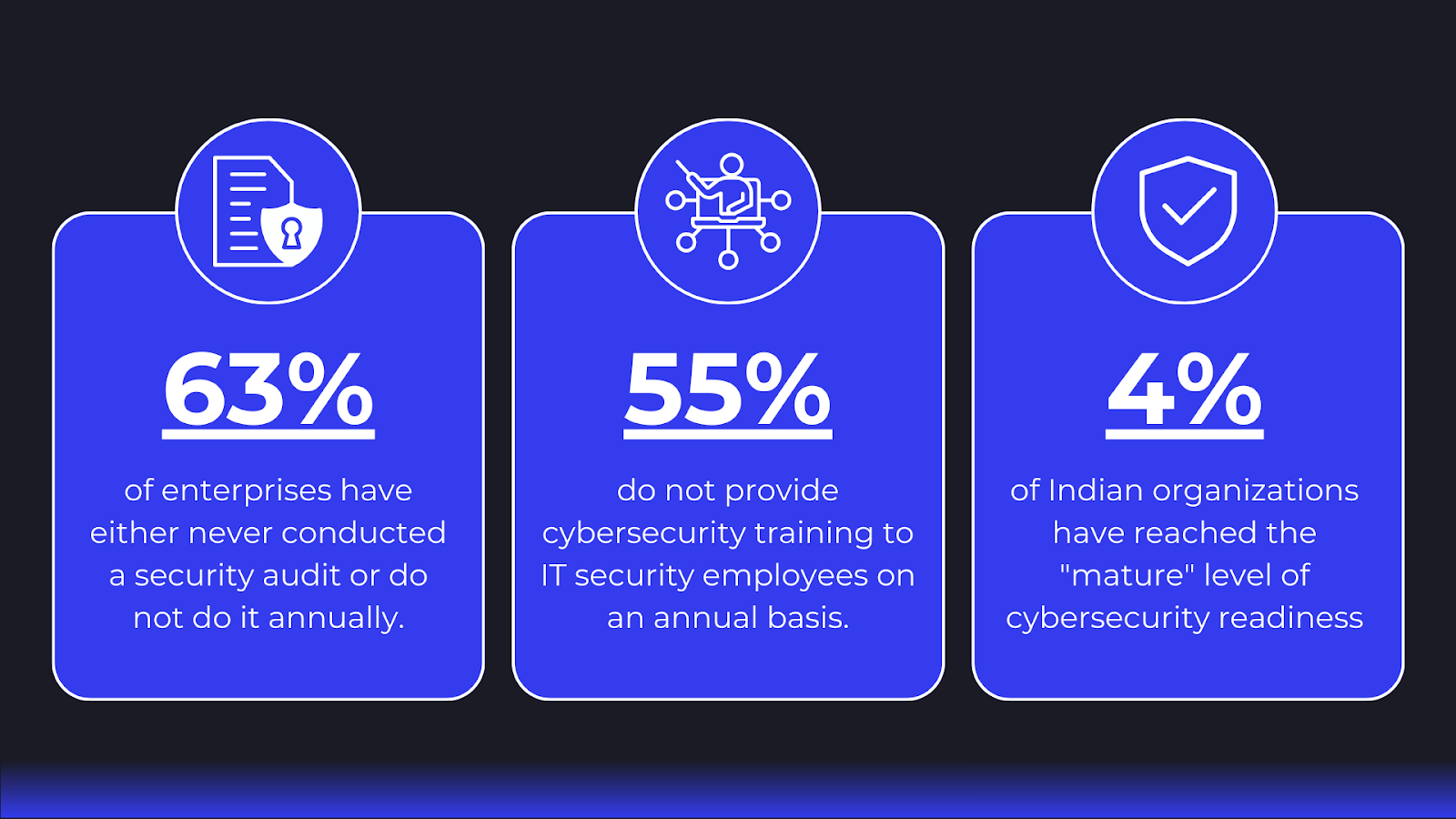
Such a meteoric rise in internet usage without a simultaneous cyber-awareness increase has led to the public availability of data of 518 million Indians (more than half of current internet users) on the dark web.
The Digital Personal Data Protection Act, passed last year, aims to prevent such violations of data privacy by holding digital data processing accountable.
The broader provisions lay the following responsibilities on enterprises as data fiduciaries and processors:

Check these analyses by Deloitte and PWC to understand them in detail.
To be compliant, data fiduciaries and processors must also take preventive action to protect all sensitive data by implementing encryption, obfuscation, tokens, access control, and detection and remediation of unauthorized access.
In the event of a personal data breach, the nature, extent, timing, location, and consequences of the breach and the security measures undertaken to mitigate it must be intimated to each affected data principal and the respective board.
In addition to the above mandates, significant data fiduciaries (most likely fintech and insurance players) must undertake annual data protection impact assessments and audits.
While these are still not finalized because they are available for feedback, the Ministry of Electronics and Information Technology has urged enterprises to begin capacity building and adaptation immediately under the provisions.
While a standard two-year transition period similar to GDPR is anticipated, it is deemed inadequate due to a multitude of factors:
Adding to this grim picture is the complex nature of modern enterprise infrastructures.
All DPDP provisions and draft rules focus on protecting personal data (boundaries of which are yet to be defined) through preventive security measures or post-breach notifications.
But how can you, as a data fiduciary or processor, do either without knowing how sensitive data is being created, handled, and delivered across your network?
Modern Enterprise Networks: Both the Problem and the Solution
Due to decentralization trends in enterprise infrastructure, questions like “Where is personal data stored?” “Who has accessed it?” and “What are we doing to protect it?” are now much more challenging to answer.
Hybrid and cloud deployments frequently replicate, cache, and store data across multi-regional nodes, making it difficult for organizations to identify where their data resides and which jurisdiction’s regulations apply.
Additionally, microservices architecture enables efficient scaling, but fragmented data flows across hundreds or thousands of components.
Tracing sensitive data manually in such environments becomes nearly impossible.
APIs, which power most of these microservices, further complicate the situation by spanning internal, external, and third-party endpoints.
This introduces risks like inconsistent data handling, unauthorized access, and regulatory non-compliance without proper governance.
However, API-first applications (currently 74% of all applications) also present an opportunity.
APIs are the backbone of modern networks, facilitating critical data exchanges between applications, databases, and external services.
When secured effectively, APIs are the closest to the data, enabling robust encryption, precise access controls, and seamless compliance monitoring across applications.
Organizations can turn APIs into a strategic asset for achieving compliance goals by adopting authentication and authorization best practices.
Automated API Security Platform Levo.ai
APIs hold immense potential to advance security and compliance initiatives, particularly for mandates like the DPDP Act. However, the lack of unified development and security practices often squanders this potential.
The following gaps in current Software Development Lifecycle (SDLC) practices hinder compliance efforts:

While rectifying such broken practices isn’t required as part of compliance adherence, it lays the foundation for an exponentially improved security and operational posture.
This approach takes security and compliance far beyond the annual audit, embedding security into your applications so you aren’t perpetually stuck in reactive mode.
While internal capacity building through hiring and training is recommended, it is not likely compelling enough to combat the pace of API integration or a stringent compliance deadline.
Utilizing automation is necessary, not an option, to save quarters’ worth of DevSecOps bandwidth and mitigate costly errors that are likely to happen through manual approaches.
Our platform streamlines the entire sensitive data detection and all recommended API security processes:
Book a demo through this link to see this in action!
Conclusion
Most enterprises will approach DPDP the hard way, scrambling close to the deadline, manually auditing systems they barely understand, and overspending by 60% or more.
The smarter move is visibility first.
Levo.ai gives you a complete picture of every API and every sensitive data flow, uncovering 90 to 250% more APIs than you knew existed without touching a single line of code. Continuous monitoring replaces annual audits. Gaps get caught before they become violations.
The deadline is coming either way. See how Levo.ai gets you ahead of it.
FAQs
What is the DPDP Act?
India's data privacy law that governs how enterprises collect, store, and protect Indian citizens' personal data. Get it wrong and you are looking at penalties exceeding ₹250 Crores plus losing trust in one of the world's fastest growing consumer markets.
Who needs to comply?
Every enterprise handling Indian citizens' data including foreign companies. Fintech and insurance firms have it harder with annual audits and impact assessments on top of the baseline requirements.
What does DPDP compliance actually require?
Encryption, tokenisation, access controls, and breach notifications to both affected individuals and your board including what happened, when, where, and what you did about it.
Why is DPDP compliance so difficult to achieve?
Most enterprises genuinely do not know where their data lives. Microservices and hybrid cloud scatter it across thousands of components. That invisibility is what makes compliance slow and expensive.
How long do enterprises have?
A two year window is expected but India's Ministry of Electronics and Information Technology is already urging enterprises not to wait. The infrastructure complexity alone makes that timeline tight.
Why do APIs matter so much here?
APIs power 74% of all applications and handle your most sensitive data exchanges. Secure them and you get encryption, access control, and continuous monitoring across every application at once.
.png)
.svg)






.png)
.png)
.png)
