Velocity was
fintech’s first MOAT
are the current



%20(1).png)









%20(1).png)







Only fintechs that secure their APIs will scale.
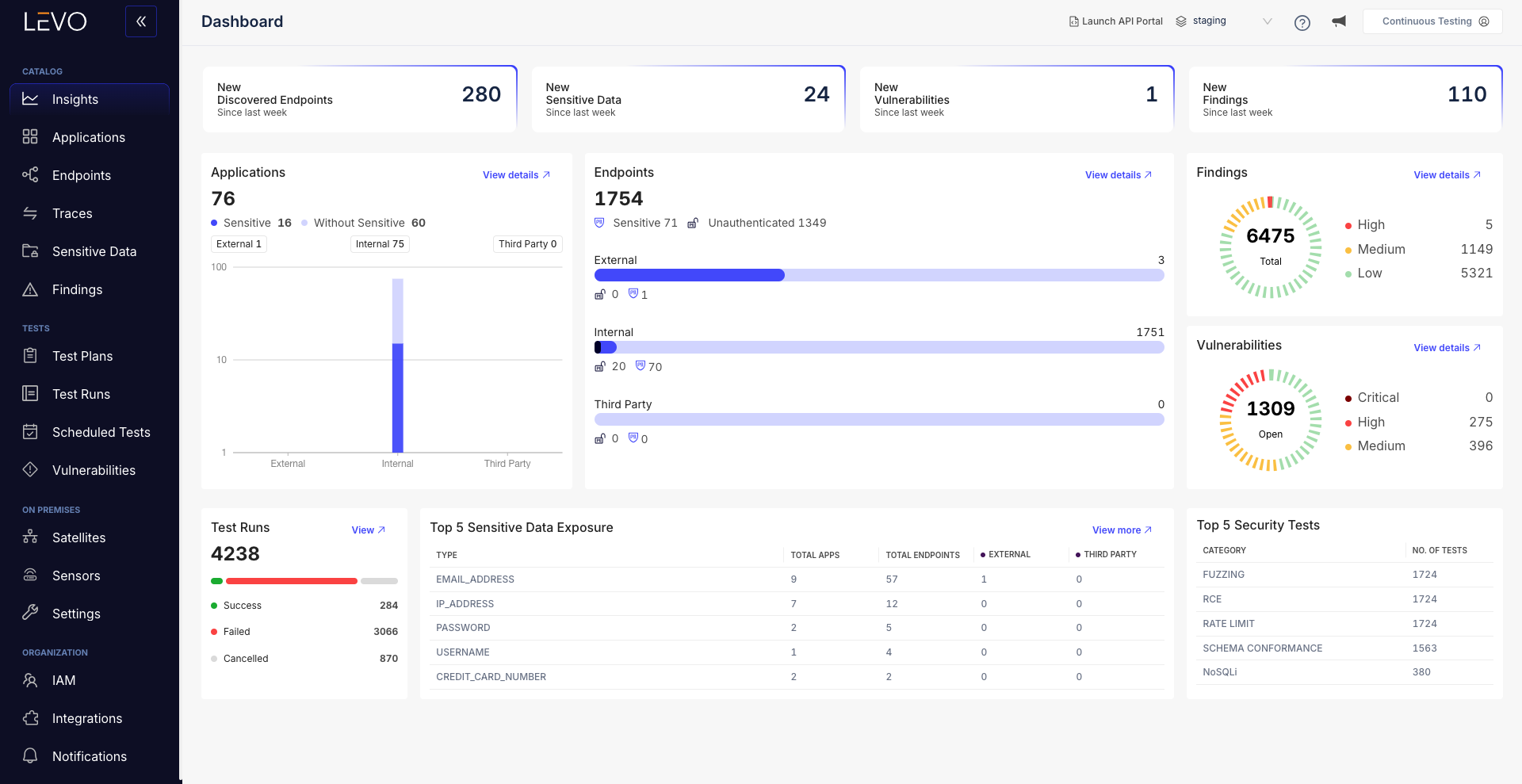
Achieve full API visibility without slowing developers
Levo continuously discovers and documents every internal, external, partner, and third-party API mapping versions, methods, auth patterns, payloads, and sensitive data flows in real-time.
Enforce strong access controls to prevent account takeovers and fraud
Levo actively monitors OAuth token scopes, consent bindings, and session validations automatically detecting drift, misuse, and unauthorized expansions.
By embedding real-time access control security testing during the build, fintechs prevent fraudulent transactions, account hijacks, and rewards abuse before they escalate.
Strong security posture without compromising velocity
Levo ensures that fintechs not only meet PCI-DSS 4.0, GDPR, SOC2, and other compliance frameworks that demand periodic security testing but also adapt to continuous deployment with continuous security testing.
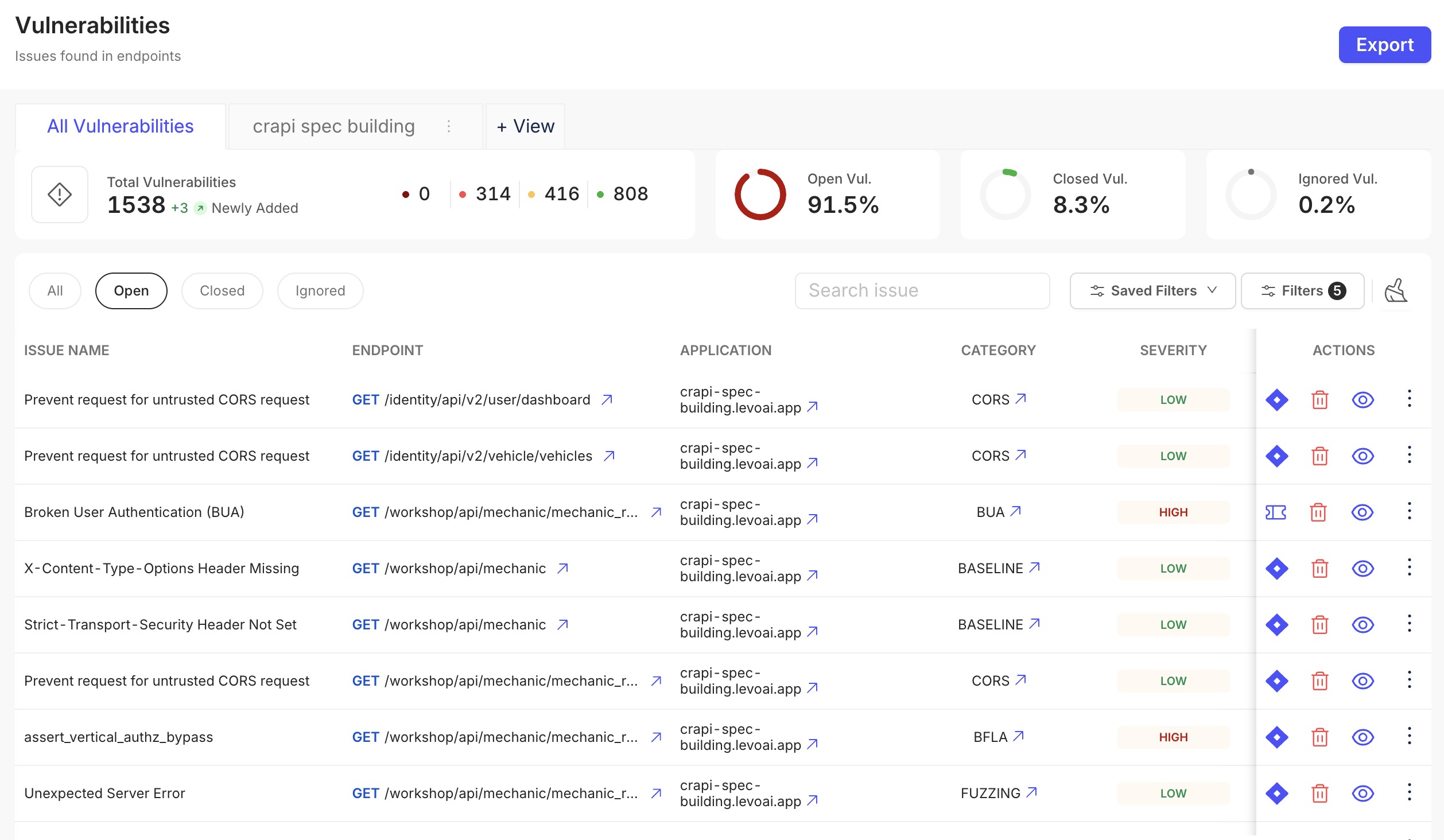
Avoid breaches and fines with prioritized vulnerability remediation
Levo identifies and prioritizes vulnerabilities based on real exploitability and sensitive data exposure. So fintech teams focus remediation efforts where customer data, revenue, and compliance exposure are highest.
Adapt monitoring to match your business, APIs, and attack patterns
Custom YAML/Python rule engines let teams define fintech-specific defense strategies as wallet APIs, aggregation platforms, and embedded finance ecosystems grow.

Lead the next fintech race
without losing the velocity that built you
Eliminate API sprawl before it triggers breaches
Levo’s eBPF-powered discovery engine continuously maps every API: external, internal, third-party, open source, zombie and shadow APIs across all environments.
It classifies exposure points handling sensitive data without strong access control all without needing any code or configuration changes.
Real-time API documentation for faster integrations
Every discovered API is instantly documented with 12+ granular parameters: versions, endpoints, methods, auth logic, payload structures, rate limits, and human-readable descriptions.
This streamlines secure partner onboarding, accelerates fintech integrations (Plaid, Stripe, embedded finance partners), and ensures APIs are ready for compliance validation without incurring developer bottlenecks or technical debt.

Launch new APIs faster without diminishing security posture
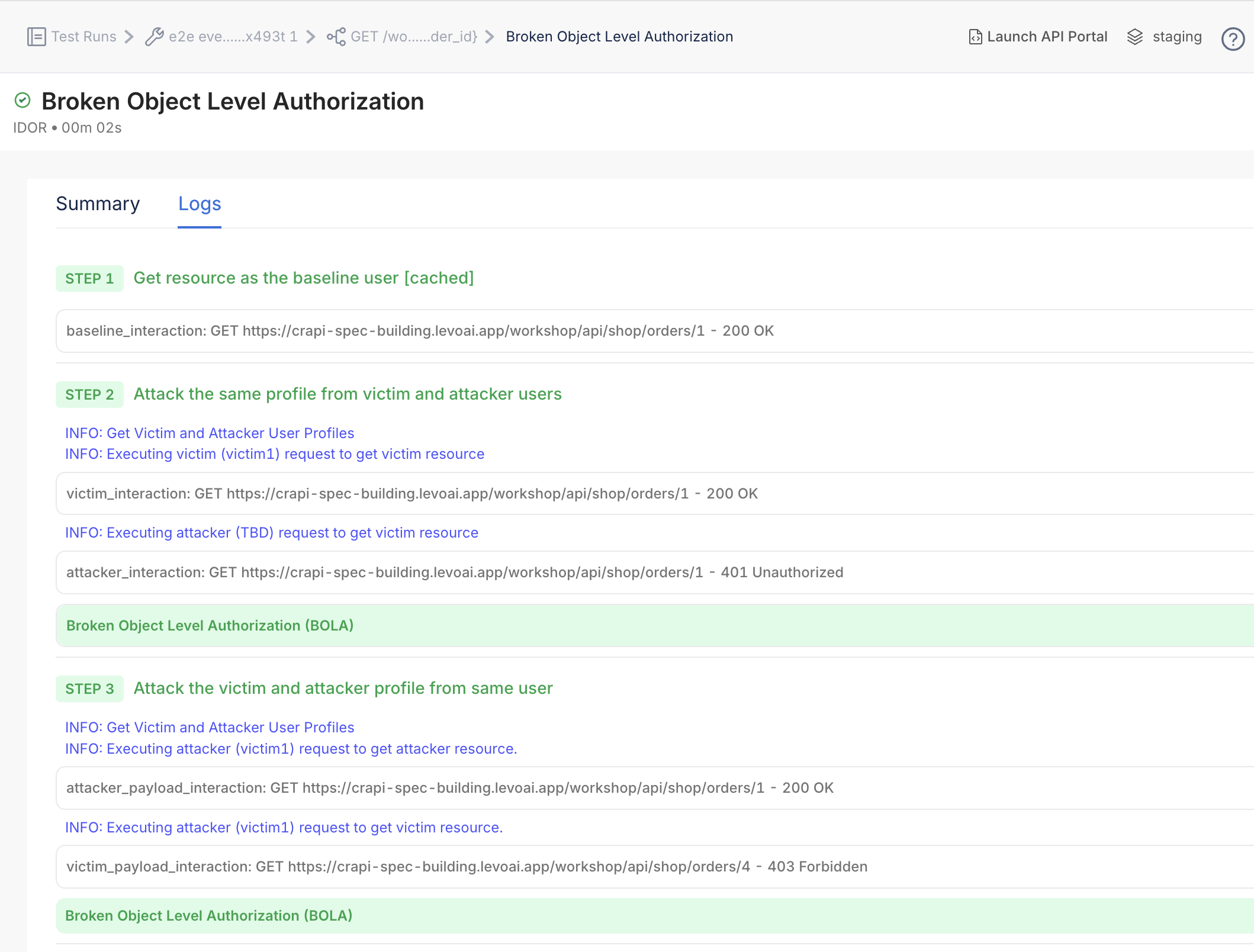
Every code merge triggers context-aware attack simulations across APIs security testing for scraping risks, token replay attacks, OAuth misconfigurations, BOLA/BFLA vulnerabilities, consent drift, and PKCE enforcement failures.
Testing is fully automated inside GitHub Actions, GitLab, Jenkins, and Bitbucket pipelines ensuring vulnerabilities are detected before release without slowing down feature launches.
Proactively protect customer data at the source
Levo automatically detects and classifies sensitive data flows (PCI DSS cardholder data, PII, account metadata, transaction details, consent artifacts) across all APIs including third-party and open integrations.
By pinpointing APIs touching critical financial information, fintechs can proactively enforce encryption, access control, tokenization, and rate limiting.

API governance success without sacrificing developer agility
Levo continuously monitors all API traffic for deviations from secure development policies. SSL inconsistencies, missing authentication headers, exposed server version leaks, improper encryption, and PII overexposures out of the box are continuously detected and surfaced.
Custom YAML/Python rule engines let security teams enforce fintech-specific governance requirements like mandatory encryption, proper CORS settings, and header validation so APIs stay compliant without manual inspection.
Lead with velocity. Win with security posture. Grow with trust.






