
Cut API bounty hunting time in half and reap more $$$! A new tool that plays well with Burp and ZAP and significantly accelerates your API bug bounty efforts.

Hacking modern web applications is all about hacking the underlying APIs being used by the mobile or web UI.
However hacking APIs is both time and resource intensive. Below is a brief description of the many steps involved.
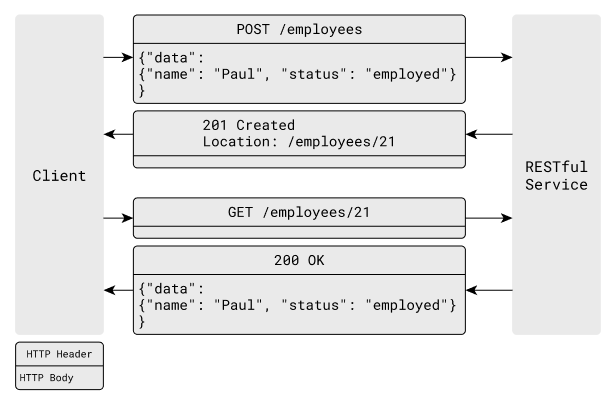
You will first need to browse the full application while proxying traffic via a tool like Burp.
Proxy API Traffic Via Burp
Then you will need to identify all the API endpoints and the underlying JSON schema by analyzing the captured traffic.
You will then have to compile all this data in a spreadsheet to keep track of it.

This is typically a multi-hour or multi-day effort based on the size and complexity of the application.
Hacking APIs is largely about trying to get unauthorized access to sensitive customer data. So ultimately you will need to comb through the APIs discovered and prioritize them based on the presence of sensitive data (PII/PSI).

Manually Identify PII In APIs
Now that you have short-listed APIs for hacking, you will need to launch various types of attacks against them using tools like Burp, Curl, Postman, etc.
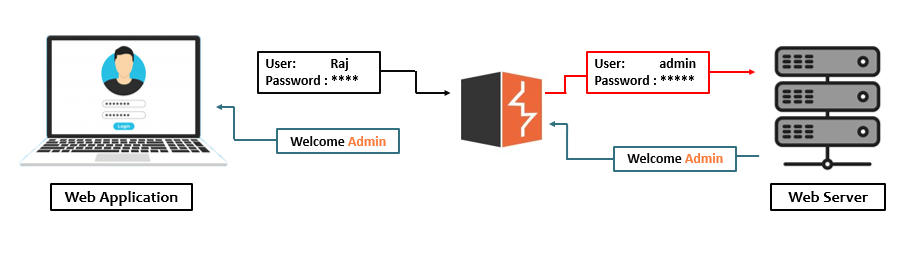
Some of the attacks involve bypassing authentication and authorization controls of the APIs. So you will need to customize Burp with addons from the marketplace, or in some cases write your own scripts to automate/scale the hacking effort.
If you are lucky, after a significant amount of work, you would have identified some API vulnerabilities that you can report, and reap a reward.

Levo Burp Extension is a completely free and open-source tool that cuts your bounty-hunting time in half.
The extension & free service, auto-discovers your API endpoints, and auto-generates the underlying OpenAPI schema for them.

In addition, the service will auto-prioritize the API endpoints based on the presence of sensitive data (PII/PSI).
All you need to do is surf the application via your Burp proxy.

Once you have auto-prioritized your API endpoints, you can use the free service to launch sophisticated business logic attacks on them.
Here is a video that shows how the extension works.
Prefer ZAP to Burp? We got you covered. Here is a ZAP plugin that essentially accomplishes the same.
We would love to hear from you about your experiences and/or any feature requests. Drop us a line at support@levo.ai
Happy bounty hunting!!